Identity
Integrate with your enterprise directory and give differing levels of access depending on need. For example, give contractors view-only access to information, while allowing the marketing team full permissions to a cloud storage service.
Allowing users unfettered access to cloud services and risky websites exposes your organization to threats, which are amplified when your sensitive data is involved. Netskope mitigates your risk by giving you control over that access, enabling you to set conditional, granular policies around employee access to both managed and unmanaged cloud services.

Take advantage of an all-mode architecture to see all of your cloud and web traffic, regardless of where your users are located or what they are using.
Maintain control over what users can do, across the web, SaaS and IaaS services and applications, to reduce your organization’s exposure to risk.
Enforce security policies, based on identity, device type, service/website, activity, and data, to best protect your organization from data exfiltration and loss.
Take advantage of an all-mode architecture to see all of your cloud and web traffic, regardless of where your users are located or what they are using.
Maintain control over what users can do, across the web, SaaS and IaaS services and applications, to reduce your organization’s exposure to risk.
Enforce security policies, based on identity, device type, service/website, activity, and data, to best protect your organization from data exfiltration and loss.
Ensure admin privileges across all services with role-based access controls, and gain visibility and control over ecosystem services connected to managed services that are used by employees.
Ensure only trusted devices access your corporate services and data. For example, set a policy that allows full access to Office 365 webmail from corporate devices while giving read-only permissions to BYOD or unmanaged devices.
Selectively grant access or govern activities based on context. With Netskope you can do things like prevent sensitive data from being downloaded onto personal devices or restrict access to a service if an employee is on an unsecured Wi-Fi network.
Ensure admin privileges across all services with role-based access controls, and gain visibility and control over ecosystem services connected to managed services that are used by employees.
Ensure only trusted devices access your corporate services and data. For example, set a policy that allows full access to Office 365 webmail from corporate devices while giving read-only permissions to BYOD or unmanaged devices.
Selectively grant access or govern activities based on context. With Netskope you can do things like prevent sensitive data from being downloaded onto personal devices or restrict access to a service if an employee is on an unsecured Wi-Fi network.
Unrivaled visibility. Real-time data and threat protection.
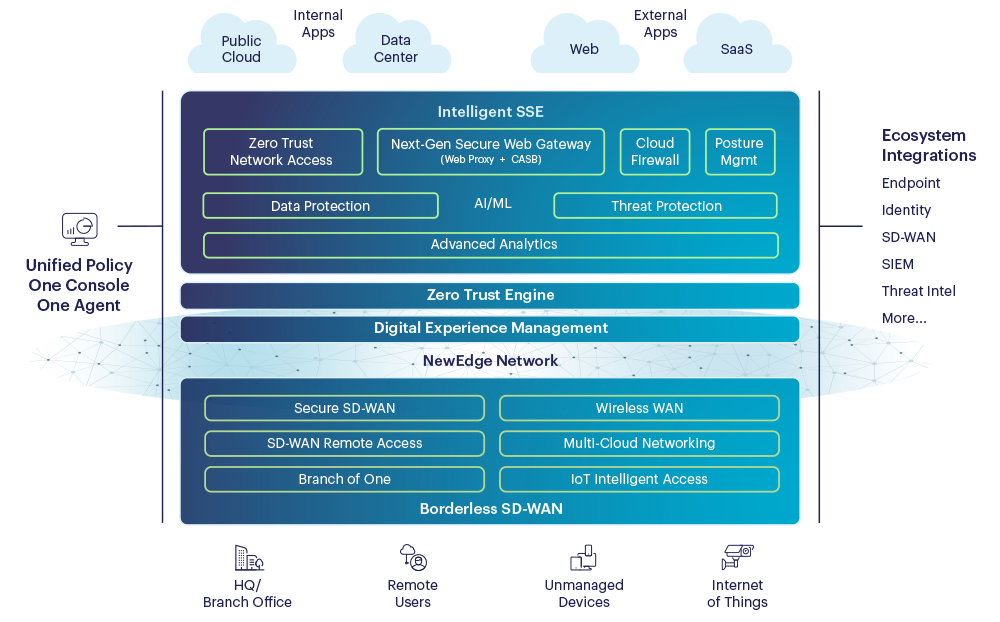
Netskope Intelligent SSE is built on the Netskope Security Cloud, a platform that provides unrivaled visibility and real-time data and threat protection when accessing cloud services, websites, and private apps from anywhere, on any device.
Cloud Exchange consumes valuable Netskope telemetry and external threat intelligence and risk scores, enabling improved policy implementation, automated service ticket creation, and exportation of log events from the Netskope Security Cloud.
We'd love to hear from you!